The AppSec Phoenix team is pleased to bring you another batch of functional additions and improvements. We are sure that you’ll find these quite interesting!
New Features
- New Licences & Freemium
- 0-Day Alerts: Application list
- Auto Creation of assets
- Time Frames for Charts
- Policy Engine (early release)
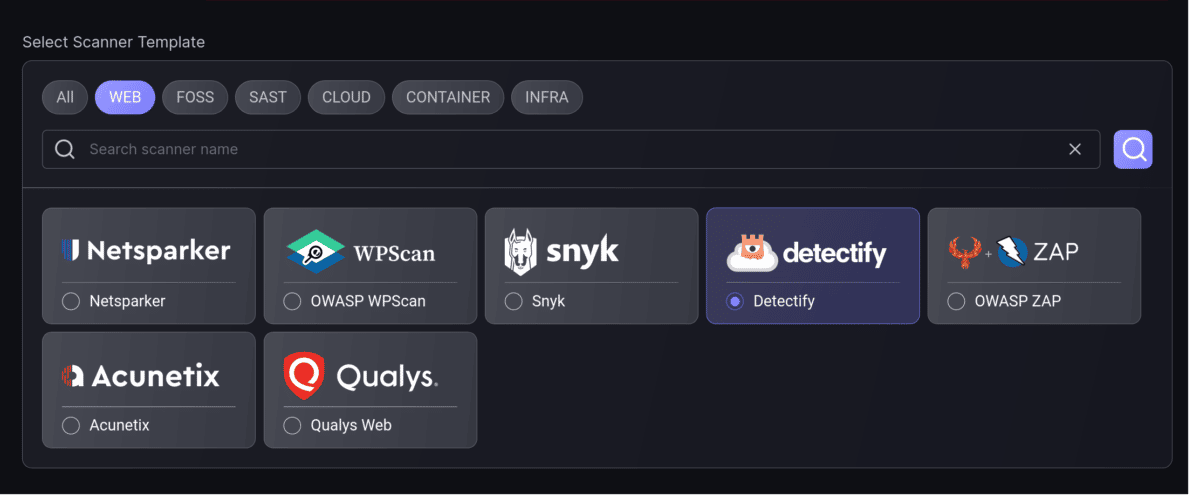
- Scanner Integrations
- Qualys Infra
- Laceworks
- Detectify
New Licensing model & trials
Now you can try the benefits of our Professional license for 14 days. Once you have reached your license limit, you’ll be presented with an option to start a 14-day trial period of our Professional license. Please see here for licence details and features.
0-Day: Affected application list
We keep improving our 0-Day alert and management functionality. Now you can get a list of all applications affected by a 0-day alert with a single clink in the alert banner. Applications display with an indication of the level of confidence of them being affected by the vulnerability.
Auto-create Components from a scanner
Configuration automation is now available in AppSec Phoenix! If you want to add all the projects/targets from a particular scanner to the same application, AppSec Phoenix will do it now for you. Automatically!
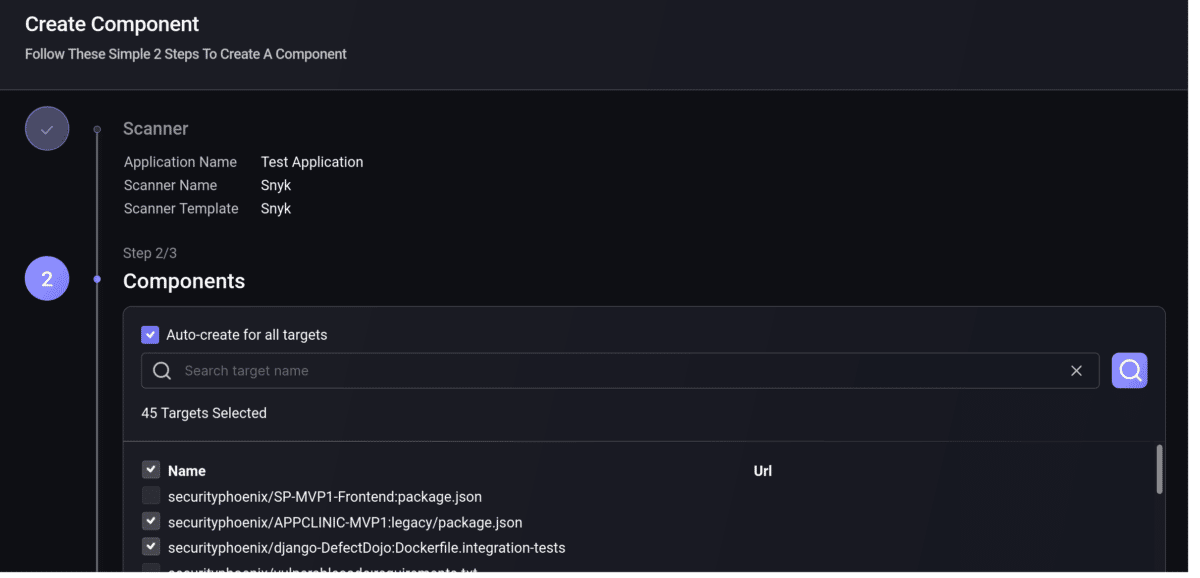
Alternatively, if you don’t want AppSec Phoenix to auto create Components but you want to select all projects/targets from your scanner, now you can do that with a single click.
Policy Engine v1 (no UI)
Our Policy Engine is coming to your account; and fast! We have started building toward a fully configurable engine to evaluate business rules and trigger actions every time that particular events take place on the platform. You’ll be able to decide when to open issue tickets for new vulnerabilities, or send alerts (and to whom) when applications change their severity score – and all this with fine-grained filters and conditions.
This first version implements some initial rules, but it’s not user-configurable yet. We’ll be adding the configuration UI and more events, conditions and actions over the next few releases. Watch this space!
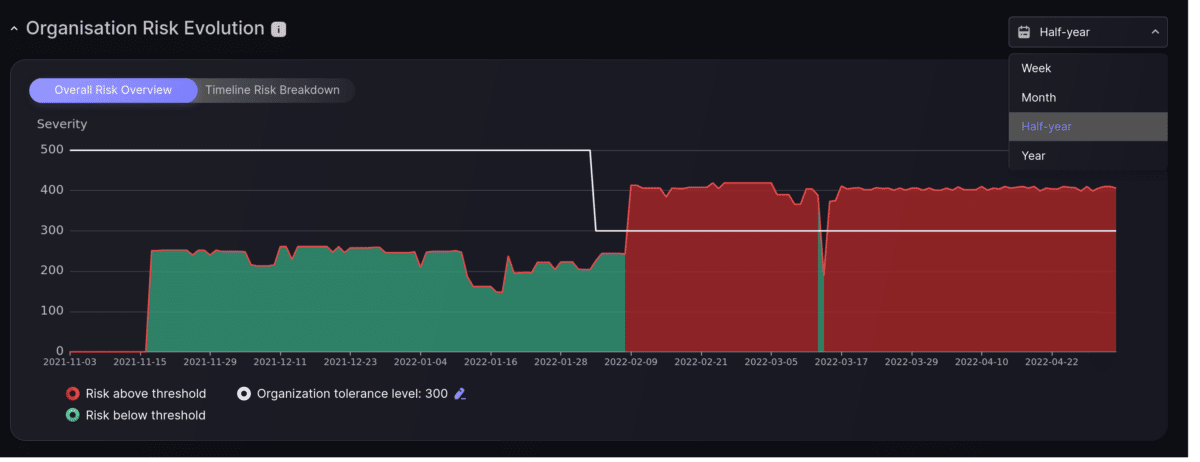
Time-frame selection for charts
Easily change the time frame that you want to see reflected in the dashboard’s charts, individually for each chart.
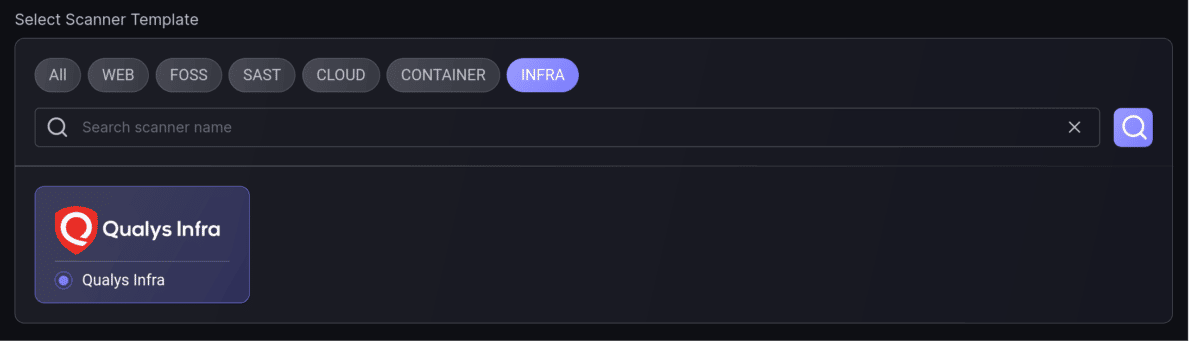
Scanner integration: Qualys Infra
To debut our support for infrastructure scanners we have released our integration with Qualys Infra. You can now connect to your Qualys account and get all your infrastructure vulnerabilities fetched and managed within AppSec Phoenix.
Watch this space for more infrastructure scanners coming up!
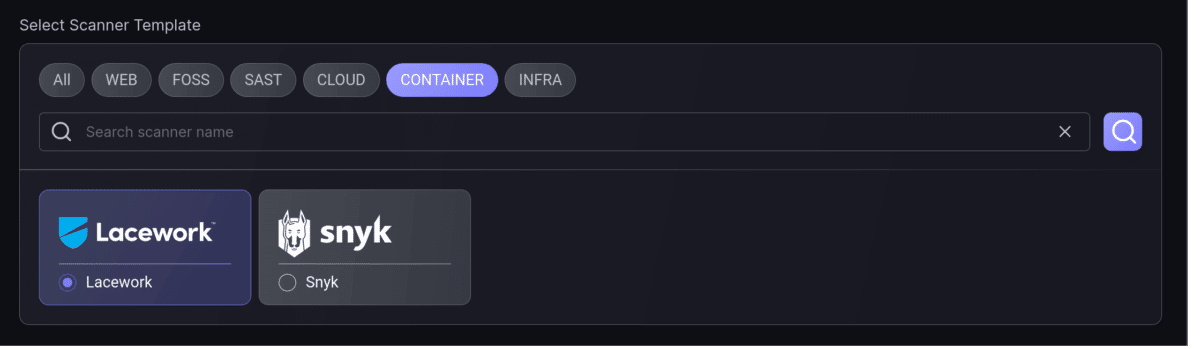
Scanner integration: Lacework (Container)
Connect to and ingest container vulnerabilities from your Lacework account for container security. No need for manual vulnerability imports; it’s all done through the native Lacework API v2.
Scanner integration: Detectify (Web)
Now you can connect directly with your Detectify account to automatically ingest all findings. As always, this is done through Detectify’s native API, so there’s a simple configuration and no need to manually import vulnerabilities.