On October 25, a critical vulnerability was announced for OpenSSL, with the fix and advisory on November 1st. This upcoming update will affect the application security and vulnerability management teams.
This is the second-rated critical vulnerability of the OpenSSL project
OpenSSL 3.0.7 update to fix Critical CVE out next Tuesday 1300-1700UTC. Does not affect versions before 3.0. https://t.co/jIRQhx0nCr
— Mark J Cox (@iamamoose) October 25, 2022
https://twitter.com/iamamoose/status/1584908434855628800
The open SSL project team announced the release of a minor version to fix the vulnerability, but it will be available on the 1st of 2022. OpenSSL 3.0.7 will patch the critical vulnerability with the disclosure of the vulnerability.
Contents
ToggleWhy a lot of attention and nervousness on this vulnerability?
In 2014, the critical Heartbleed bug was announced and fixed; it became obvious how many systems depend on this vulnerability and how long it took for all the systems to be aligned to this new version.
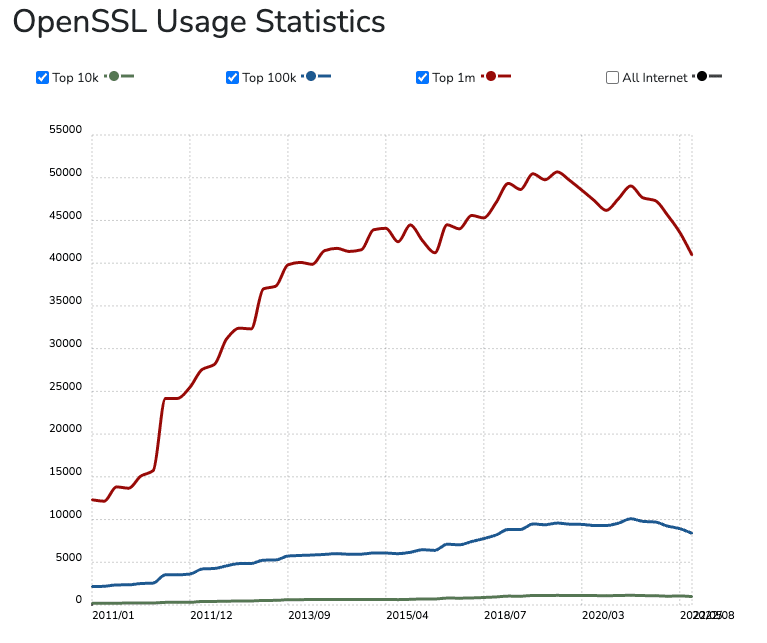
As OpenSSL is a widespread library, shown below is just a fraction of the direct usage:
After log4j software composition analysis and infrastructure, the composition is ever more critical.
The challenge with OpenSSL is that is nested in a lot of systems and a lot of libraries.
So while you might be safe on an Operating system (not using openssl), the container that runs on it or the embedded software might expose and use
Controversial announcement
The patch for the critical vulnerability was announced on october 25th weeks before the official patch.
Tweet: https://twitter.com/iamamoose/status/1584908434855628800
OpenSSL 3.0.7 update to fix Critical CVE out next Tuesday 1300-1700UTC. Does not affect versions before 3.0. https://t.co/jIRQhx0nCr
— Mark J Cox (@iamamoose) October 25, 2022
This allowed the team to gear up and prepare for fixes. There is a debate that this behaviour could trigger attackers to exploit the vulnerability https://twitter.com/__agwa/status/1584916997472751618
This will be OpenSSL’s first “CRITICAL” vulnerability since 2016. Examples of “CRITICAL” vulnerabilities include “significant disclosure of the contents of server memory (potentially revealing user details), … https://t.co/fsykqaovvY
— Andrew Ayer (@__agwa) October 25, 2022
System Affected
OpenSSL is included in many operating systems (Windows, macOS, various Linux distributions, etc.); client-side software; web and email server software (Apache, nginx, etc.); network appliances (Cisco, Fortinet, Juniper, etc.), industrial control systems, and so on.
Best defence
As this is an RCE, the best way to defend is to
1 – create an inventory of all the systems that have open SSL installed and could have open SSL installed.
2 – fix as many instances as possible, prioritizing the one that can access easily
3 – for systems, repo that can’t be immediately fixed (vendors, SLA, maintenance), apply virtual patches on a WAF level to prevent specific strings from triggering the vulnerability. as there is no advisory in this space on the specific string, stay tuned for further updates
Challenges with those types of libraries
The challenge with open-source libraries, log4j, for example, is that a relatively small pool of people maintains them for free. This is quickly changing, with Google pledging large amounts of money to fix open-source libraries.
Key Point of this vulnerability:
- The vulnerability seems to affect only OpenSSL 3.x releases, if you’re not using OpenSSL 3.x (ie, you’re still on OpenSSL 1.x across your org), you might be OK. Ensure your inventory is well maintained to determine whether you’re affected.
- If you have systems which use OpenSSL 3.x that are Internet-facing or run critical functions (authn, authz), consider putting some mitigation in place ahead of this. Ex: if TLS termination occurs on a system which uses OpenSSL 3.x, consider delegating TLS termination to a system with a different TLS stack till you can patch.
- If you have vendors who may use OpenSSL, now is the time to inquire whether they use 3.x releases and their errata schedule. Also list all the vendors that might have OpenSSL
use: openssl s_client -connect <domain name or IP>:<port>- Consider instituting a change freeze on/around November 1 to allow your teams the opportunity to build/test/release/patch as your highest priority if you’re using OpenSSL 3.x
- OpenSSL is a library. Libraries can be linked to statically or dynamically. Consider how you would patch your systems in both cases.
- * Any software upgrade, including dependent libraries, must go through testing. Complex distributed systems are hard. Make no assumptions about how a “trivial” patch may affect your systems.
- * In case your systems use OpenSSL 3.x, how would you address static vs dynamically linked programs? What mitigation and patch strategies do you have?
- What are your playbooks if a breach occurs prior to completing your mitigation or patch strategy? Work with your leadership team to understand your options for each scenario. Documenting scenarios and viable paths help to avoid rash decisions in stressful situations.
- * During the log4j firefight, we saw numerous security commenters jump on the vulnerability, spreading misinformation and asking to remove libraries.
- This can cause a lot more pain, and removing a component can cause an enormous ripple effect.
- Fixing a vulnerability in code or on a system should always be staged, tested and verified with proper regression testing. Allow enough time for this implementing mitigating countermeasures like virtual patching.
Best of luck to all the security team and development team working on this
Previous Issues of vulnerability Weekly
- Security Vulnerability of the Week 3/10/22 – Application Security – Cloud – Vulnerability – Exchange Zero Day & Mitigations, bitbucket, cobalt stike
- Security Vulnerability of the Week 12/09/22 – Application Security – Cloud Security – Linux Malware, Windows patched 64 vulns with zero-day, Uber Hack Timeline, GTA 6/Rockstar Hack – This week we deep dive into Linux Malware, Windows patched 64 vuln with zero-day, Uber Hack Timeline, GTA 6/Rockstar Hack
- Security Vulnerability of the Week 12/09/22 – Application Security – Uber Hack Timeline – Special Focus on Uber latest news on hack
- Security Vulnerability Weekly 22/08/22 – Apple Vulnerability, Android Bugdrop Vulnerability, WordPress, CISA, and recent Hacks to Mailchimp and Twilio – Apple Vulnerability, CISA new vulnerability for September, Bugdrop new android vulnerabilities, recent hacks to twilio exposing digital ocaean clients and Mailchimp hack
- Security Vulnerability of the Week 08/08/22 – Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more




















