Vandana’s leadership and year of field experience in cybersecurity strengthen the leadership and provide a sounding board for the community.
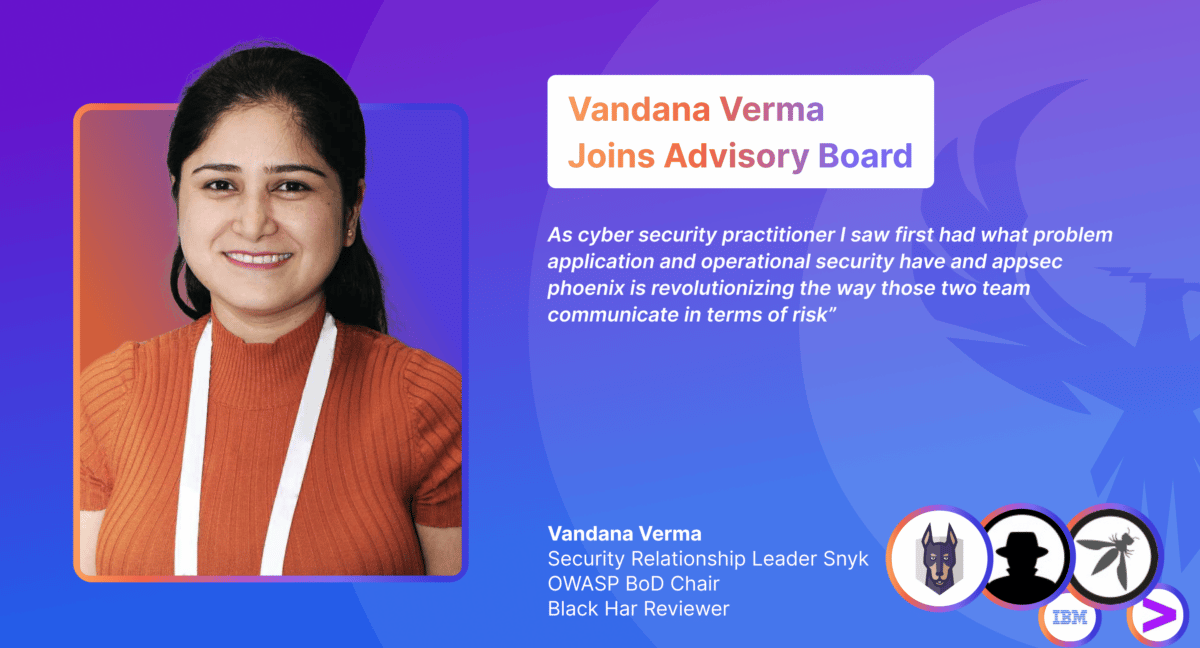
LONDON, England (September 28, 2022)— AppSec Phoenix, the next-gen leader in Vulnerability and Posture Management for Cloud and Application security, has announced the addition of Vandana Verma to its Technology Advisory Board. Vandana joins the firm as an advisor adding to the board years of leadership and experience.
Vandana is a well-respected leader in the OWASP and Application security community. Vandana is the Security Relations at SNYK, co-founder at infosec Kids and OWASP Chair of the OWASP Board of directors. Vandana is on the review board of Black Hat and CISO Magazine and was previously Security Solution Architect at IBM. Vandana is a pillar of the security community and a well-respected member.
“We are honoured and enthusiastic to welcome Vandana in the Phoenix Security family and welcome her years of experience in the technology advisory board,” said Francesco Cipollone, CEO and founder of AppSec Phoenix. “Vandana has the unique combination of direct approach, kindness and keen eye on the community that we need to have a thriving board.”
Francesco Cipollone
“I am thrilled to be part of AppSec Phoenix’s advisory board and keen to see it part of the OWASP community,” said Vandana ” As a cyber security practitioner, I saw first-hand what problem application and operational security have, and Phoenix Security is revolutionizing the way those two teams communicate in terms of risk.”
Vandana Verma
Vandana joins an advisory board that boasts several notable names in the cybersecurity sector, including:
- Andrew Peterson led Signal Science, a leading cybersecurity product, for five years before it sold to Fastly for $775M. Peterson brings startup knowledge, international support, exposure to the US market, and key introductions to customers. His insight into the American market and its current trends and his contacts with venture capitalists provide valuable insight to the advisory team. He also advises several companies and has been instrumental in providing Security Phoenix with key recommendations on getting a head start in product startup and potential pitfalls.
- Christopher Hodson is an acclaimed leader, advisor, and investor with over a decade of experience in the tech and cybersecurity sectors. Christopher has a board leadership track record, has served as CISO for Zscaler and Tanium, and is currently at Contentful. Christopher is also a seasoned board executive, serving as a board advisor for Charted Institute of Information Security, CompTIA, and Cybrary.
- Chris Romeo is an acclaimed leader, advisor, and investor with over twenty-five years of experience in the application and cybersecurity sectors. Chris Romeo is the Chief Security Officer and co-founder of Security Journey and is a leading voice and thinker in application security, threat modelling, and security culture. Chris is the host of the award-winning “Application Security Podcast” and is a highly rated industry speaker and trainer, featured at the RSA Conference, the AppSec Village @ DefCon, OWASP Global AppSec, ISC2 Security Congress, and All Day DevOps.
- Xabi Errotabehere has more than 20 years of experience building world-class digital products. He co-founded Cloud Conformity, a Cloud Security Posture Management tool, and took the company in a high-growth mode before Trend Micro acquired it in 2019. Errotabehere brings insight into how to successfully manage a business in its early days and techniques to effectively go to market and acquire clients.
- Mike is a well-respected leader and advisor. Mike Takla is the co-founder & CRO of Hacknotice, previously, he was the Director of Inside Sales at Security Scorecard. His several years of field and practical experience have given mike the best insight on how to measure and run teams.
To learn more about AppSec Phoenix or to schedule a free demo, visit https://www.phoenix.security/request-a-demo/.